Microsoft recently announced security improvements to Azure Active Directory (AAD), allowing IT administrators to review and remove inactive user accounts that might pose a safety risk. Admins can now delete accounts from AAD that haven’t logged in to Microsoft’s cloud-based identity and access management service for a pre-determined amount of time.
This guide explains the benefits of finding and removing inactive AAD accounts, clarifies the process, and outlines why you should invest in a full-service consultant to get more value from this feature.
Finding and Removing Inactive AAD Accounts, Explained
IT admins can now identify and delete accounts that haven’t logged into Azure Active Directory for a certain number of days. This new feature, part of AAD’s Identify Governance service, prevents unauthorized users like former employees and contractors from accessing your sensitive information.
“In large environments, user accounts are not always deleted when employees leave an organization,” says Microsoft on its website. “As an IT administrator, you want to detect and handle these obsolete user accounts because they represent a security risk.”
Finding and removing inactive Azure Active Directory accounts is a relatively simple process for most users:
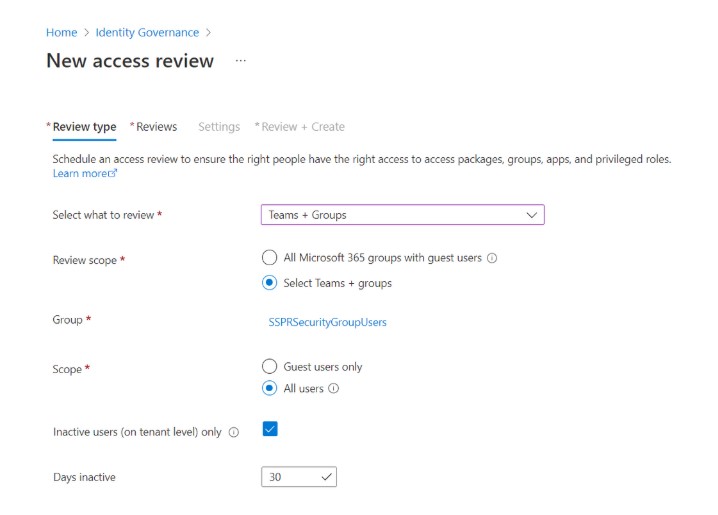
- You’ll need to access your AAD portal, head over to the Identify Governance blade, and then the New Access Review tab.
- Here, you can review all Microsoft 365 groups with guest users or specific teams and groups.
- Next, tick the Inactive Users (On Tenant Level Only) box and specify how long inactive accounts should be allowed to access your information.
- AAD will remove accounts that have been inactive for the number of days or months you choose (up to 2 years).
- For example, ADD will delete inactive accounts that have been inactive for 30 days.
Read more: Azure Identity: Who Are You and What Do You Want?
What Are the Benefits of This New Feature?
AAD’s new feature brings multiple security benefits to your organization:
Prevent Security Vulnerabilities
Employees and contractors are the No. 1 cause of data breaches, and 56 percent of security professionals say insider threats are becoming more common. When a worker leaves your organization, for whatever reason, there’s always a risk that person will continue to access your business information, share it with a competitor, sell it to hackers, or do something else nefarious.
AAD’s new feature prevents former employees and contractors from logging into AAD and viewing your information, providing you with ongoing peace of mind. Getting rid of unused accounts will prevent security vulnerabilities in the future.
Cleanse Data
Finding and removing inactive accounts enables admins to set security parameters for accounts, flag those accounts for review, and remove them through automation. Cleansing the data of inactive users prevents security risks and ensures that only authorized persons can access your resources on AAD. You can also assign reviewers for redundancy before deleting user accounts.
Review Access to Applications That Integrate With AAD
Microsoft doesn’t just enable you to remove inactive users from AAD but review user access to any applications that integrate with the service via connectors. That helps you manage identity and access across the Microsoft ecosystem and, again, prevent unauthorized persons from getting their hands on your data.
Read more: Why Use Azure Functions to Facilitate Data Integration Development Patterns?
What Else You Need to Know
AAD’s new feature isn’t available for all businesses that use the service. You’ll need an Azure AD Premium P2 license if you want to find and remove inactive accounts. Working with a reputable Microsoft consultant can ensure you have the requirements for this feature and help you define the right security parameters for managing inactive AAD accounts and users.
Dynamic Consultants Group (DCG) are experts in Microsoft business application consulting and help you navigate and optimize the Microsoft products and services used in your enterprise, including Azure Active Directory. The company has over 150 customers and partners worldwide and helped over 1 million people. DCG understands that no one solution works for every enterprise, so it tailors services around your industry and business model.
Final Word
Access and identity have become a huge concern for enterprises that manage temporary contractors, hire and fire employees, and grow and merge with other organizations. When workers leave a company, managers need to handle ever-complex security environments and ensure former employees and contractors can’t access sensitive information. Finding and deleting inactive accounts on Azure Active Directory can help with this process, enabling companies to set account parameters and automatically remove obsolete users after a pre-determined amount of time.
DCG is a full-service Microsoft consultancy that provides more value when managing inactive accounts in AAD. A consultant will work hard to help you learn whether you have the correct license for Microsoft’s new feature and define security parameters for AAD users. Schedule a Teams meeting with DCG today!